HOME | DD
 rendercomics — Restart 0026
rendercomics — Restart 0026

#3d #biosuit #comic #drone #hacking #computer #postapocalyptic #survival
Published: 2019-04-25 12:57:35 +0000 UTC; Views: 1079; Favourites: 7; Downloads: 0
Redirect to original
Description
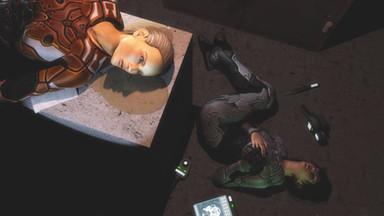
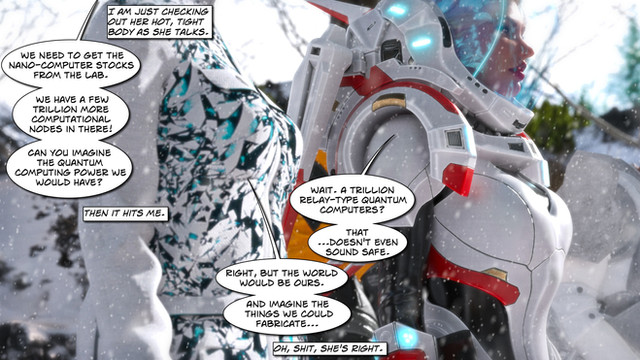
A very tight, fun series of events here, and Shade's reaction is fun - she doesn't know what to think back there. Eli is trying her best to fight back by being smart. Was the resume thing a trick by Eli to make Relay just as culpable in hacking the drone? Eli knows all too well about the danger of Relay's automatic updates, so that may be another weapon she is using in this fight - she knows those will auto download and apply.At the root of it, Eli is just trying to get Relay's help in wiping the drone's logs - but does she need to? Could she do this herself? Smart readers will notice another layer to this all and I am starting to wonder if Eli isn't social hacking Relay to make her more cooperative - without brute force hacking Relay's systems.
There is also turning out to be a difference between local communication between connected devices (like WiFi) and this new "long range" communication the drone needs and Relay is using now to phone home (like a Cell network). This will be explained further but I wanted to mention it now in case people wonder what the difference is.
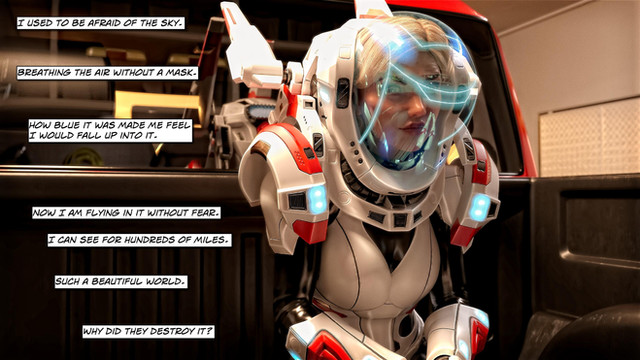
And Ghost Jesus is back. I love Eli's fun-house mirror view of religion. It is respectful while still pointing out the absurdity of the notion of faith and spirits in Eli's mind.
Related content
Comments: 5

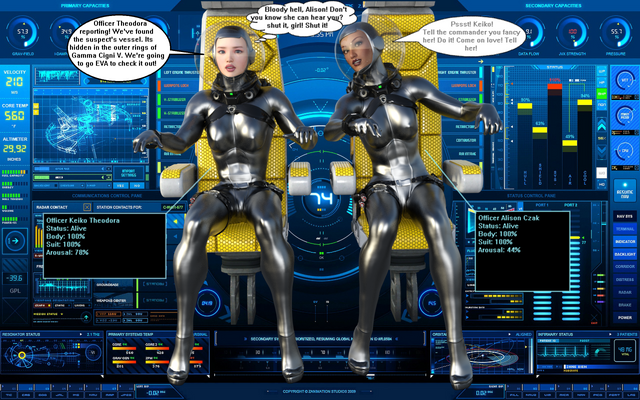
True, in a sense. Relay was 'stored' in the syringe, strange to think, and when Relay came online that pulled in patches and updates from local systems around Eli - like a local Bittorrent scattering of files and updates. Relay could also pull in information from connected devices and local safe zones, based on local data from environmental systems and other factors.
In the Internet world, there are secure socket systems that ensure who you are talking to is who you are talking to, and encode the streams so a 'man in the middle' attack can't occur, like someone injecting a virus into an executable you are downloading.
Relay is probably programmed to seek out updates from secure servers as soon as communication is established - you are correct that it has been 30 years and the unknown network at this point is the status of these secure servers for the M2CIP.co company. Who knows their status and who controls them now? Eli, in a sense, doesn't have a choice, Relay will try to update anyways so Eli might as well use this as leverage against Relay and the system to get help with the drone.
Also, in the software world, there are checksums and other safeguards on operating system files that ensure what is downloaded is supposed to be safe and correct for the hardware. Chromebooks have these protections and check every OS file on reboot. I am assuming Relay has similar verification systems for the files being pulled in. Also, if the checksums do not match for what you receive you can assume a 'man in the middle' attack is happening.
But if a malicious function was inserted at the corporate level Relay or Eli would not know. But then again, that is a fact we live with every day with the devices we place trust in.
👍: 0 ⏩: 0